What does a simultaneously dead and not-dead cat have to do with cybersecurity?
Quite a bit, as it turns out. Schrödinger’s quantum kitty is the key to encryption that, while probably not totally unbreakable (can we assume anything is), can make it a whole lot harder for the bad guys to decrypt confidential material.
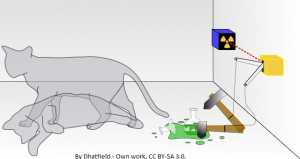 For those unacquainted with the feline, Schrödinger’s Cat was a 1935 thought experiment conducted by Austrian physicist Erwin Schrödinger to illustrate his ideas on one theory of quantum mechanics. In it, a cat, a flask of poison, and a radioactive source are placed in a box, along with a detector. If even a single radioactive particle is seen to be decaying, the flask is broken and the poison kills the cat. The theory, known as the Copenhagen interpretation, suggests that at some point the cat is both alive and dead, yet if the box is opened, it contains either an alive or a dead cat. The act of looking affects the outcome. That of course sparked a number of interpretations and ideas for additional experiments. And over the years, different models of quantum computing have arisen as well.
For those unacquainted with the feline, Schrödinger’s Cat was a 1935 thought experiment conducted by Austrian physicist Erwin Schrödinger to illustrate his ideas on one theory of quantum mechanics. In it, a cat, a flask of poison, and a radioactive source are placed in a box, along with a detector. If even a single radioactive particle is seen to be decaying, the flask is broken and the poison kills the cat. The theory, known as the Copenhagen interpretation, suggests that at some point the cat is both alive and dead, yet if the box is opened, it contains either an alive or a dead cat. The act of looking affects the outcome. That of course sparked a number of interpretations and ideas for additional experiments. And over the years, different models of quantum computing have arisen as well.
Security experts have also realized that there are applications for quantum computing in encryption. They can both make things more secure, and, unfortunately, also expose weaknesses in current encryption methods.
Today’s encryption relies on some heavy-duty mathematics to generate keys and encode data. But as computing power has gotten cheaper, it’s become easier and easier to perform brute-force attacks that solve those math problems. That means that some types of encryption such as DES, RC4, and MD5 are now to be avoided because they’re too easy to break.
Our quantum kitty solves the problem. It’s both dead and alive, until someone peeks into the box. Similarly, a quantum encryption key, which is generated not with mathematics but with physics, only remains in its original state as long as no-one looks at it. If a hacker tries to steal the key, the very act of looking at it changes it and alerts the sender that it’s been compromised.
In a paper published by the SANS Institute, author Bruce Aubum explains it this way:
“It is as if I mail a book to a friend, and someone in the post office opens the package and reads the book, and all of the letters become scrambled and the book is rendered unreadable. Furthermore, the book cannot be put back to the way it was. Now the book is of no use to the recipient, but it can be seen that someone broke into the package.”
Quantum keys have been in limited use for over a decade, but there are problems. The keys are created by sending a series of photons in various states (there are four possibilities), translating those states into computer-readable binary numbers (patterns of zeros and ones), and using the resulting code as a key. But the physics of the technology limit the distance over which the key can be sent – so far, up to 250 miles – and that’s not good enough. Work continues.
Quantum computers also put many of today’s encryption techniques at risk. Because they are able to factor very large numbers that our digital computers have trouble with, they can break previously unbreakable keys. Now in addition to worrying about the mathematical factors, analysts are looking at whether encryption schemes are resistant to quantum computing attacks.
But don’t panic yet. In its post on next generation security, Cisco notes, “As of October 2015, there has been attention on quantum computers (QCs) and their potential impact on current cryptography standards. Although practical QCs would pose a threat to crypto standards for public-key infrastructure (PKI) key exchange and encryption, no one has demonstrated a practical quantum computer yet. It is an area of active research and growing interest. Although it is possible, it can’t be said with certainty whether practical QCs will be built in the future. An algorithm that would be secure even after a QC is built is said to have postquantum security or be quantum computer resistant (QCR). AES-256, SHA-384, and SHA-512 are believed to have postquantum security. There are public key algorithms that are believed to have postquantum security too, but there are no standards for their use in Internet protocols yet.”
The operative word, of course, is “yet”. As quantum computing moves from science project to mainstream technology, standards bodies will be forced to act, or the industry will act for them, creating de-facto standards just as it did with modem technologies two decades ago. But, as with modems, if things are left to develop on their own, there will be a period of fragmentation and confusion before there’s agreement.
The industry is also looking for standards in current cryptography that are quantum-resistant. The US National Institute of Standards and Technology (NIST) is currently accepting submissions for quantum-resistant cryptographic algorithms (the deadline is November 30, 2017), under an initiative dubbed the post-quantum cryptography project. At the same time, NIST is engaged in quantum computing and cryptography research.
It’s all very much a work in progress, but it highlights one thing: cybersecurity is a moving target, and quantum computing and cryptography have the potential to make things both more and less secure. Which is somehow appropriate, given the simultaneously dead and not-dead cat that started it all.









What types of data are quantumly encrypted?